Simulator of nsF5 embedding (Matlab)
Description
The algorithm nsF5 evolved from the F5 algorithm originally proposed by Andreas Westfeld in 2001 [9]. F5 decreases the absolute value of DCT coefficients and incorporates matrix embedding - a coding scheme that decreases the number of changes and consequently increases the steganographic security. F5 embeds only into nonzero AC DCT coefficients; if a coefficient becomes zero after embedding (the so called shrinkage), the same bit is reembedded at the next coefficient. Shrinkage substantially decreases the embedding efficiency as the values +1 and -1 are the most frequent nonzero DCT coefficients in natural images.
The effect of shrinkage can be alleviated by applying more sophisticated coding schemes, such as wet paper codes (WPC) [3] or syndrome trellis codes (STC) [1]. The algorithm nsF5 was introduced in 2007 [4] as an improved version of F5, alleviating the negative effect of shrinkage by using wet paper codes [3]. See the publication [4] for more details.
The theoretical bound on the embedding efficiency of the nsF5 algorithm is known to be equal to
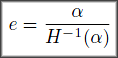
where alpha is the relative payload with respect to the number of changeable coefficients (the number of nonzero AC DCT coefficients in the image) and H-1 stands for the inverse of the binary entropy function. For research purposes, in order to study the embedding impact of the nsF5 algorithm, it is sufficient to use a simulation of the algorithm that mimics the statistical impact on DCT coefficients. In other words, from a given value of the embedding efficiency e, one can easily calculate the number of embedding changes that nsF5 would introduce.
In most of our previously published papers, including [4], [5], [6], and [7], we tested nsF5 by simulating its impact with embedding efficiency of WPCs taken from [3]. However, the recently proposed STCs [1] can achieve higher embedding efficiency and thus allow us to get much closer to the theoretical bound in practice than WPCs did. The experimental values of embedding efficiency taken from [3] thus no longer correspond to the real steganographic security of nsF5 - with better codes, the security of nsF5 slightly increased. Therefore, we suggest to use the theoretical bound of embedding efficiency given by the formula above for all future experiments for studying and/or evaluating the steganographic security of the nsF5 algorithm, as STCs can already get pretty close to the bound (see for example [2], Figure 4).
Based on the arguments stated in the previous paragraph, we provide an implementation of the nsF5 algorithm that uses the theoretical bound for the embedding efficiency as we believe this is the right way nsF5 should be simulated, even though it is not comparable with our previously published works. As of June 2011, we switched to the implementation provided at this website for our future research.
Thank you.
Contact
- Jessica Fridrich - fridrich (at) binghamton (dot) edu
- Jan Kodovský - jan (dot) kodovsky (at) binghamton (dot) edu
Download
- - Dependency: you will need
Phil Sallee's Matlab JPEG toolbox(functions jpeg_read and jpeg_write). Update: the website is no longer active. With the author's permission, we provide the copy of relevant files (including a few pre-compiled verions) here. - - Download: nsf5_simulation.zip (includes the main file nsf5_simulation.m, an introductory example file
test.m, and a few pre-compiled versions of functions jpeg_read and jpeg_write)
References
[1] T. Filler, J. Judas, and J. Fridrich, Minimizing additive distortion in steganography using Syndrome-Trellis Codes. IEEE Transactions on Information Forensics and Security, vol.PP, no.99, pp.1, 2011.
[2] T. Filler and J. Fridrich, Design of adaptive steganographic schemes for digital images. In N. D. Memon, E. J. Delp, P. W. Wong, and J. Dittmann, editors, Proceedings SPIE, Electronic Imaging, Security and Forensics of Multimedia XIII, volume 7880, San Francisco, CA, January 23–26, 2011.
[3] J. Fridrich, M. Goljan, and D. Soukal, Wet paper codes with improved embedding efficiency. IEEE Transactions on Information Forensics and Security, 1(1):102–110, 2006.
[4] J. Fridrich, T. Pevný, and J. Kodovský, Statistically undetectable JPEG steganography: Dead ends, challenges, and opportunities. In J. Dittmann and J. Fridrich, editors, Proceedings of the 9th ACM Multimedia & Security Workshop, pages 3–14, Dallas, TX, September 20–21, 2007.
[5] J. Kodovský and J. Fridrich, Calibration revisited . In J. Dittmann, S. Craver, and J. Fridrich, editors, Proceedings of the 11th ACM Multimedia & Security Workshop, pages 63–74, Princeton, NJ, September 7–8, 2009.
[6] J. Kodovský, T. Pevný, and J. Fridrich, Modern steganalysis can detect YASS. In N. D. Memon, E. J. Delp, P. W. Wong, and J. Dittmann, editors, Proceedings SPIE, Electronic Imaging, Security and Forensics of Multimedia XII, volume 7541, pages 02–01–02–11, San Jose, CA, January 17–21, 2010.
[7] J. Kodovský and J. Fridrich, Steganalysis in high dimensions: Fusing classifiers built on random subspaces. In N. D. Memon, E. J. Delp, P. W. Wong, and J. Dittmann, editors, Proceedings SPIE, Electronic Imaging, Security and Forensics of Multimedia XIII, volume 7880, pages OL 1–13, San Francisco, CA, January 23–26, 2011.
[8] J. Kodovský, J. Fridrich, and V. Holub, Ensemble classifiers for steganalysis of digital media. Submitted to IEEE Transactions on Information Forensics and Security, currently under review.
[9] A. Westfeld, High capacity despite better steganalysis (F5—a steganographic algorithm). In I.S. Moskowitz, editor, Information Hiding, 4th International Workshop, volume 2137 of Lecture Notes in Computer Science, pages 289–302. Springer-Verlag, New York, 2001.